Unified Credentials Access Platform UCAP Malaysia
What is Unified Credentials Access Platform – UCAP?
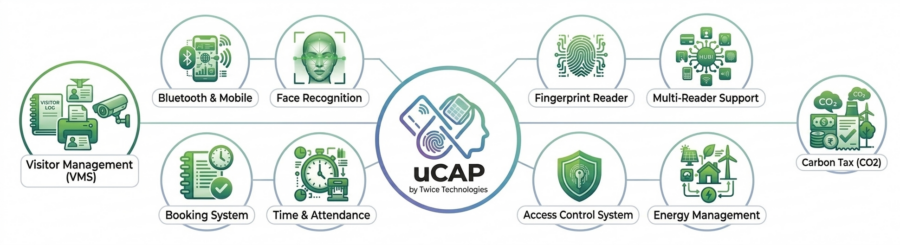
Fragmented access control systems across multiple vendors, legacy hardware, and locations create security gaps and operational inefficiencies. The Unified Credential Access Platform (uCAP) by Twice Technologies is the most advanced cloud-based solution and on-premises solution that unifies multi-PACS systems into a single platform.
With digital wallet credentials, centralized management, and real-time analytics, uCAP improves security visibility, reduces cost, and simplifies access control across multiple sites.
Unified Your Security Systems Into One Intelligent Platform
Break free from fragmented access control, biometric systems, and legacy infrastructure. UCAP (Unified Credential Access Platform) centralizes everything into one powerful, secure dashboard. Key Focus: Interoperability, long-term sustainability, and controlled modernization
- Avoid single vendor lock-in
uCAP supports integration with multi-vendor hardware and software (access control devices, biometrics, identity systems), allowing agencies to avoid dependency on a single supplier and maintain procurement flexibility. - Legacy system maintenance
Enables continued use of existing infrastructure (older controllers, card systems, databases) by integrating them into a unified platform, reducing the need for full system replacement. - Phased system upgrades
Supports gradual modernization agencies can upgrade buildings, departments, or subsystems in stages without disrupting operations or requiring a complete overhaul. - Centralized identity & access governance
Single platform to manage staff, contractors, and visitors across ministries, departments, and facilities with role-based access control. - Audit & compliance readiness
Detailed access logs and reporting support regulatory requirements, internal audits, and incident investigations.
Is Your Security System Holding You Back?
Many organizations today operate with fragmented access control systems built over time—often combining multiple vendors, legacy hardware, and site-specific configurations. While functional, this approach introduces significant limitations that directly impact security, efficiency, and scalability.
Disconnected Systems Across Multiple Vendors
Most enterprises rely on different Physical Access Control Systems (PACS) across sites. These systems often operate in silos, with no centralized integration layer. As a result:
- Security teams must manage multiple platforms and interfaces
- Data is inconsistent and difficult to synchronize
- Integration with other systems (HR, surveillance, visitor management) becomes complex
This lack of interoperability reduces the effectiveness of your overall security ecosystem.
Limited Visibility Across Locations
Without a unified credentials access platform, organizations lack real-time visibility into user access, events, and system status across different sites. This leads to:
- Delayed incident response due to fragmented monitoring
- Inability to track user movement across multiple locations
- Difficulty in generating centralized reports and insights
In critical environments such as data centers, banking, or multi-branch operations, this creates serious operational blind spots.
Manual Processes and Operational Inefficiencies
Many legacy access control systems still depend on manual workflows for:
- User provisioning and de-provisioning
- Card issuance and replacement
- Access level configuration
These processes are time-consuming, error-prone, and heavily dependent on IT or security personnel. As organizations scale, this leads to:
- Increased administrative overhead
- Higher risk of human error
- Slower response to access requests and changes
Compliance Risks and Poor Audit Tracking
Regulatory compliance requires accurate audit trails and controlled access management. However, fragmented systems often lack:
- Centralized logging and reporting
- Consistent audit trails across all sites
- Real-time monitoring for compliance breaches
This makes it difficult to meet industry standards and increases exposure to:
- Security incidents
- Regulatory penalties
- Internal governance failures
The Hidden Impact: Security Blind Spots & Increased Risk
When these challenges combine, they create critical gaps in your security posture:
- Unauthorized access may go undetected
- Delayed response to incidents
- Lack of accountability across systems
Ultimately, organizations face higher operational risk, increased costs, and reduced confidence in their security infrastructure.
UCAP – One Platform. Total Control.
A modern unified credentials access platform is essential to eliminate these inefficiencies and provide centralized, intelligent security management across all locations
“From reactive security to proactive intelligence”.
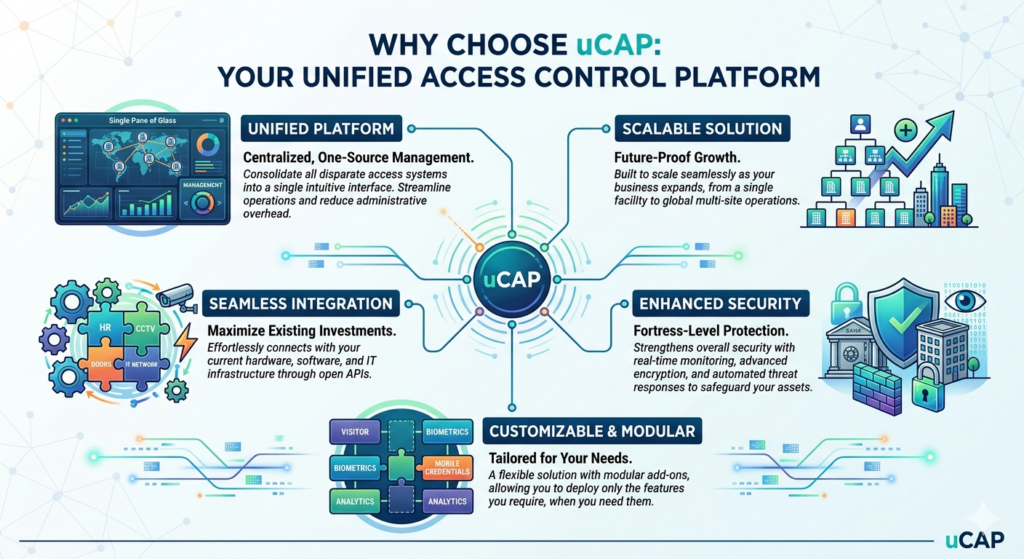
Why Choose uCAP?
Eliminate Operational Blind Spots
Traditional access control systems operate in silos, limiting visibility across locations and creating gaps in security monitoring. uCAP introduces a centralized command layer that consolidates all access events, user activities, and system statuses into a single dashboard.
With real-time monitoring and intelligent analytics, security teams can:
- Track access events across multiple sites instantly
- Identify anomalies and unauthorized access attempts
- Respond faster to incidents with complete situational awareness
This unified visibility eliminates blind spots and strengthens your overall security posture.
Seamless Multi-Brand Integration
Many organizations face challenges managing different Physical Access Control Systems (PACS) from multiple vendors. Replacing existing infrastructure is costly and disruptive.
uCAP is designed with multi-PACS integration capabilities, allowing you to:
- Connect and unify existing systems regardless of brand
- Extend the lifespan of legacy hardware
- Avoid vendor lock-in and maintain flexibility
This ensures a smooth transition to a modern access control platform without major capital investment.
Enterprise-Level Compliance & Audit Readiness
Maintaining compliance with global security and data protection standards is critical for enterprise environments. uCAP provides built-in tools to support regulatory requirements, including:
- GDPR – Secure handling and management of personal data
- HIPAA – Protection of sensitive healthcare information
- PCI DSS – Secure processing of payment-related data
With centralized logging, detailed audit trails, and real-time reporting, organizations can:
- Maintain full visibility of access history
- Simplify compliance audits
- Reduce the risk of regulatory penalties
Scalable for Enterprise Growth
As organizations expand, managing access control across multiple locations becomes increasingly complex. uCAP is built on a scalable architecture that supports growth without compromising performance or security.
Whether you operate a single facility or a multi-site enterprise, uCAP enables:
- Centralized management of all locations from one platform
- Easy onboarding of new sites, users, and devices
- Flexible deployment options (cloud, on-premise, or hybrid)
This ensures your access control system evolves alongside your business needs.
uCAP – Powerful Features Designed for Modern Security
Centralized Cardholder Management
- Add, edit, and remove users easily
- Assign access levels and permissions
- Track user activity across all sites
Advanced Biometric Authentication
- Fingerprint recognition
- Facial recognition
- Iris scanning
- Secure and fraud-resistant
Real-Time Reporting Dashboard
- Live monitoring of access events
- Customizable reports
- Data-driven decision making
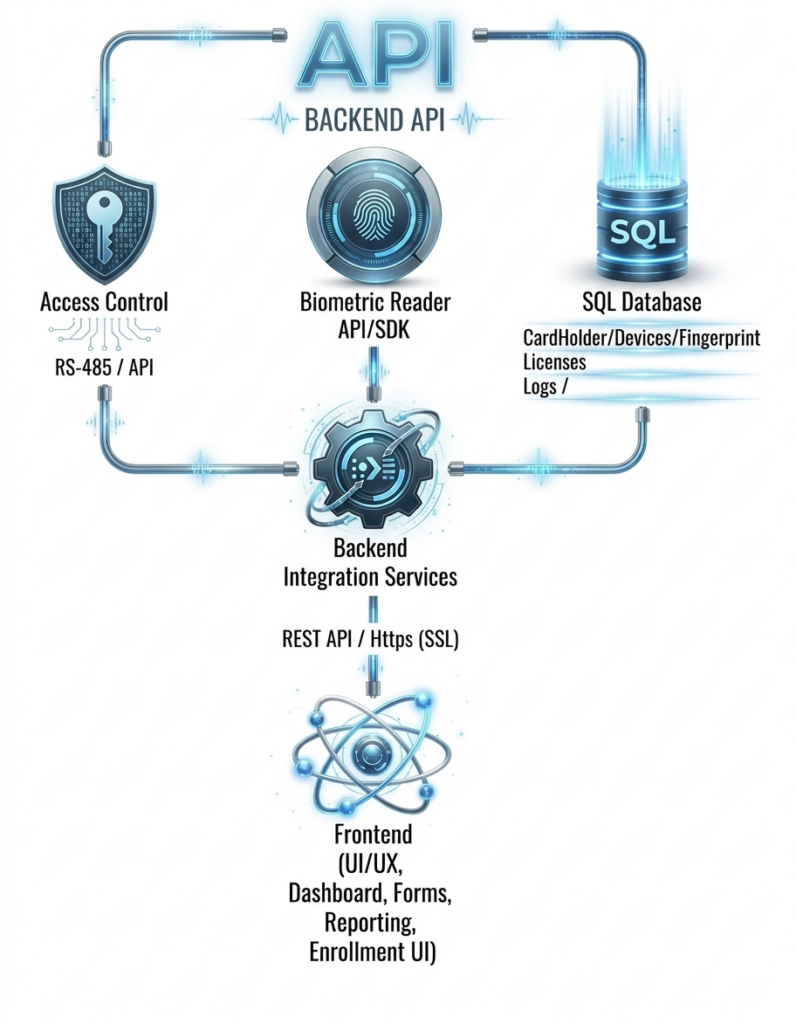
uCAP – Built for Security, Performance, and Integration
uCAP is designed with a modern, modular architecture:
- Web-based user interface
- Secure backend API
- Integration layer for third-party systems
- Centralized and secure database
- Built-in compliance framework
Client References
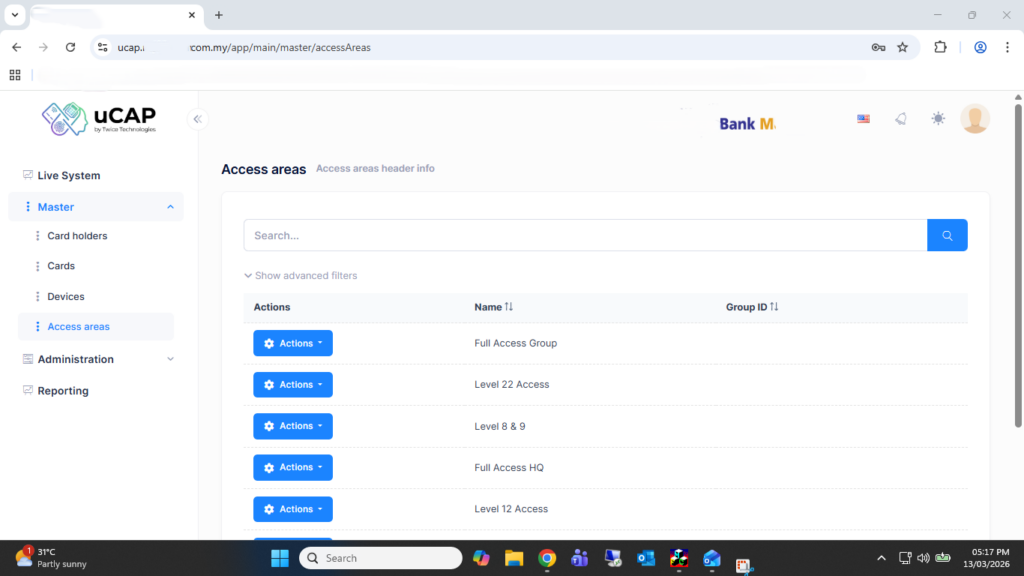
UCAP IMPLEMENTATION IN LOCAL BANK IN MALAYSIA
Bank M implemented our Unified Credentials Access Platform to centrally manage access control across multiple floors and turnstile entry points, integrating both biometric authentication fingerprint and card-based credentials. This unified system enhances security by ensuring only authorized personnel can access designated areas, while also streamlining user management under a single platform. The backend card access system that been used in is Vanderbilt ACT Pro Enterprise.
As part of their nationwide expansion strategy, the solution is being rolled out across all branches in Malaysia. The deployment is designed with a hybrid architecture, combining cloud-based management with on-premises infrastructure. This allows the headquarters to maintain centralized oversight, real-time monitoring, and data synchronization, while each branch retains operational resilience even in the event of network disruptions.
The platform enables Bank M to efficiently manage staff access by branch, department, and role, with configurable access levels and time-based permissions. It also provides comprehensive reporting and audit trails, supporting compliance requirements and internal security policies. Additionally, features such as automated user provisioning, remote management, and system scalability ensure that the bank can adapt quickly to organizational growth and evolving security needs.
Overall, this implementation not only strengthens physical security across all locations but also improves operational efficiency, visibility, and control over workforce access management nationwide.